What Is Nonpublic Personal Information (NPI)?
·
17 min read
If you work in financial services, you likely deal with nonpublic personal information (NPI) every day. Account details, application data, and transaction records all fall into a category that regulators take seriously.
For fintechs and other regulated financial companies, NPI touches product design, data access, vendor relationships, and regulatory exams. Understanding it early helps teams navigate those areas with more clarity over time.
This article breaks down what nonpublic personal information actually means, what doesn’t count as NPI, and where confusion often arises. It also highlights how NPI connects to real compliance decisions, not just policy language.
At InnReg, we help financial services firms identify what qualifies as nonpublic personal information and apply NPI requirements across onboarding, account data, transaction records, and vendor access. Our team also provides support with GLBA and Regulation S-P.
Nonpublic Personal Information (NPI) Definition
Nonpublic personal information (NPI) is personally identifiable financial information that isn’t publicly available. Financial institutions often collect this information when they provide products or services to their customers.
In simple terms, NPI is information a customer gives you, or that you generate about them, because they’re using your financial product. That can include:
Data collected during onboarding
Information created through transactions
Details obtained from third parties as part of providing services.
For example, when a customer applies for an account and shares their Social Security number, income details, or account numbers, that information is NPI. If your system later creates transaction histories or account balances tied to that customer, those records are also NPI, even though the customer didn’t type them in directly.
What matters most is context. If the information identifies an individual and relates to their financial relationship with your company, regulators will almost always treat it as nonpublic personal information.
What Is Not Considered NPI
Information is generally not considered NPI if it’s publicly available.
That includes data from government records, public websites, or widely distributed publications, as long as your company didn’t combine it with nonpublic financial details. For example, a customer’s name and business address listed on a public registry wouldn’t be NPI on its own.
Aggregated or anonymized data also falls outside the NPI category when it can’t reasonably be linked back to an individual. Usage statistics, trend reports, or high-level analytics that strip out personal identifiers are common examples.
Context still matters. Public information can become NPI if it’s tied to a customer’s financial relationship with your company. For instance, a publicly listed phone number connected to a specific account record may still be treated as NPI because of how it’s used.
Knowing where that line sits helps teams mitigate accidental compliance gaps.
What Are Examples of Nonpublic Personal Information?
Nonpublic personal information covers a wide range of data that financial companies collect and create. Common examples of NPI include:
Names, addresses, and contact details provided during onboarding
Social Security numbers, tax identification numbers, and government-issued IDs
Account numbers, routing numbers, and card details
Transaction histories, balances, and payment activity
Income information, credit data, and employment details
NPI also includes information that your systems generate over time. For example, a customer’s trading history, loan payment record, or wallet activity is still NPI, even though it wasn’t directly submitted by the customer.
It’s also worth noting that NPI isn’t limited to individuals. In some cases, information about small business owners or sole proprietors can qualify as NPI when it’s tied to a personal financial relationship.
NPI vs. Related Data Types
Nonpublic personal information often gets mixed up with other data categories. The differences matter because each type comes with different compliance expectations and risk levels.
Here’s a quick overview of how nonpublic personal information compares to other common data types and why those distinctions matter for compliance.
NPI vs. PII
NPI and Personally Identifiable Information (PII) often overlap, but they aren’t the same thing. PII is a broader concept, while NPI is specific to financial relationships and regulated financial institutions.
PII includes information that can identify a person, such as a name, email address, or phone number. That information may or may not be sensitive on its own. For example, an email address collected for a marketing newsletter is PII, but it isn’t automatically NPI.
NPI, on the other hand, is tied to a person’s financial relationship with your company. When that same email address is linked to an investment account, loan, or payment activity, it becomes NPI because of the financial context.
Data Type | What It Covers | Example |
|---|---|---|
PII | Information that can identify an individual, regardless of context | Name and phone number collected for event registration |
NPI | Nonpublic personal information tied to a financial product or service | Name and phone number linked to a brokerage account |
NPI vs. Public Information
Public information may identify a person, but that doesn’t automatically make it nonpublic personal information. The key difference is whether the information is publicly available and how your company uses it.
For example, a home purchase recorded in a county registry is public information, even though it relates to a financial transaction. If you store that home purchase record inside a customer profile or use it to make credit or suitability decisions, regulators may treat it as NPI because of the context.
NPI vs. Confidential Business Information
NPI focuses on consumers, while confidential business information is about the company itself. They’re protected for different reasons and under different rules, even though both are essential.
Confidential business information includes things like:
Pricing models
Internal forecasts
Source code
Strategic plans.
For example, your firm’s trading algorithms or product roadmap are confidential business information, not NPI.
See also:
NPI vs. Non-Private Information
“Non-private information” isn’t a formal regulatory term, but people use it a lot. It’s usually meant to describe information that isn’t sensitive, confidential, or subject to specific privacy rules.
In most cases, people use “non-private information” to refer to public or low-risk data. That might include marketing content, generalized product information, or high-level statistics that don’t identify an individual. For example, a public interest rate posted on your website would typically be called non-private information.
The risk comes from treating this phrase as a real classification. Regulators don’t recognize “non-private information” as a defined category. If data identifies a person and relates to a financial relationship, calling it non-private doesn’t change how it’s regulated.
The safest approach is to avoid relying on informal labels. Teams should focus on whether information is public, personal, or financial, and apply controls based on that reality rather than shorthand terms.

Need help with fintech compliance?
Fill out the form below and our experts will get back to you.
Laws and Regulations Governing NPI
When handling NPI, it’s important to understand the legal frameworks that govern how it can be collected, used, and protected. Nonpublic personal information is regulated under several overlapping laws and rules, and the requirements that apply depend on your business model, your regulators, and where your customers are located.
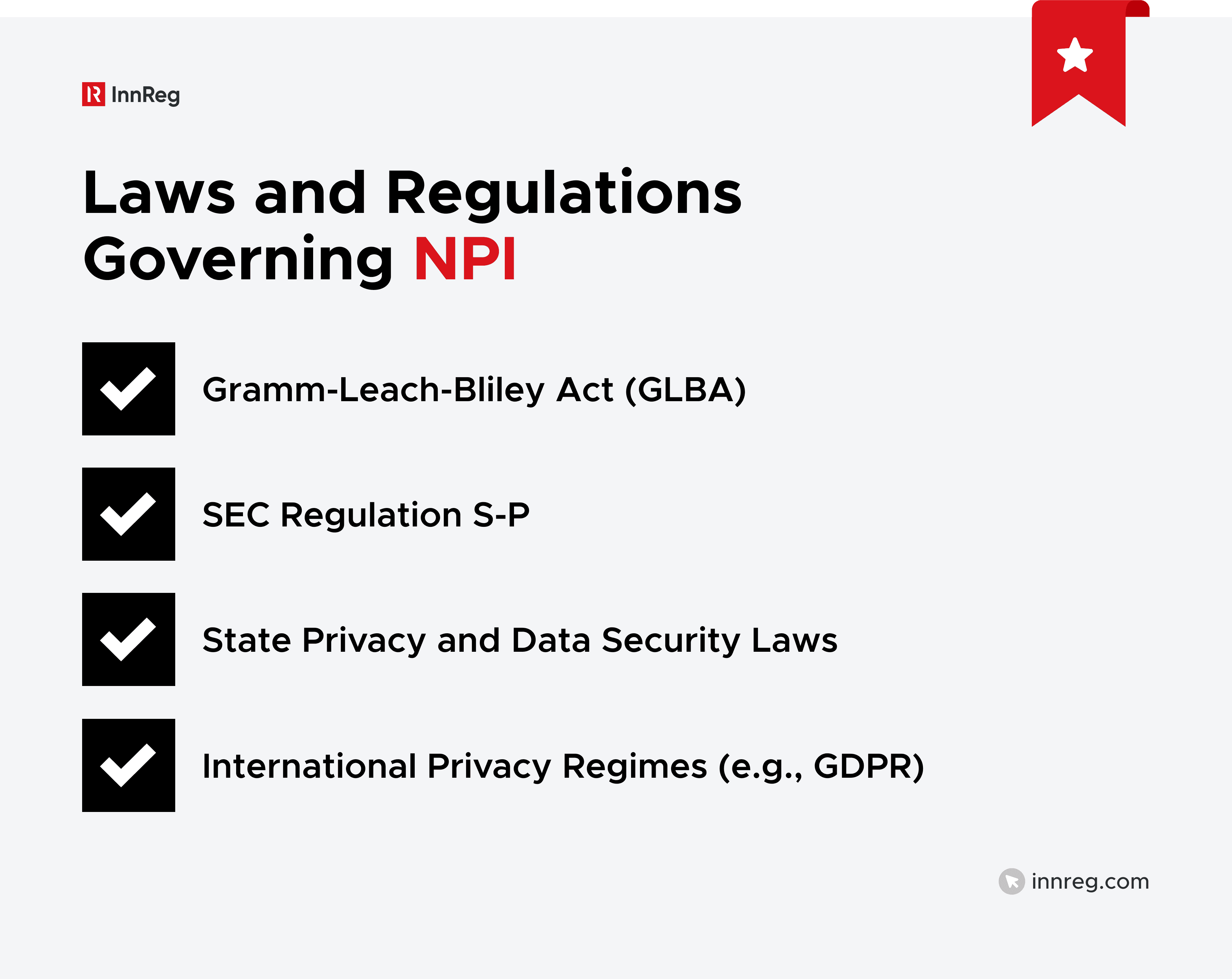
Gramm-Leach-Bliley Act (GLBA)
The Gramm-Leach-Bliley Act, often referred to as GLBA, is the primary US law governing NPI in financial services. It applies to financial institutions that collect or use consumer financial data, including many fintechs, not just traditional banks.
GLBA focuses on two core ideas:
Customers should understand how their information is used.
Companies should protect that information from unauthorized access.
For example, a lender collecting income and credit data during an application process falls squarely under GLBA.
Many fintechs run into trouble by assuming GLBA only applies to banks. In reality, broker-dealers, investment firms, payment companies, and other regulated entities often fall within its scope.
GLBA Privacy Rule
The GLBA Privacy Rule focuses on how financial institutions collect, use, and share NPI. It also sets expectations for what customers should be told about those practices.
At a high level, the rule requires companies to provide clear privacy notices that explain what information is collected and how it’s shared. For example, if a fintech shares customer data with service providers for processing or analytics, that practice should be disclosed in its privacy notice.
The Privacy Rule also gives consumers certain rights, including the ability to opt out of some types of data sharing.
GLBA Safeguards Rule
The GLBA Safeguards Rule is about how companies protect NPI, not just what they say in their privacy notices. It requires financial institutions to maintain a written information security program that fits their size, complexity, and data risks.
This often means putting controls around how NPI is accessed, stored, and shared. For example, limiting customer data access to employees who need it for their roles is a basic expectation, not an advanced security measure.
The rule doesn’t prescribe specific tools or technologies. Instead, it expects companies to assess their risks and implement reasonable administrative, technical, and physical safeguards. For fintechs, that often includes access controls, incident response planning, and vendor oversight that reflects how data actually flows through the business.
For a deeper understanding of the Gramm-Leach-Bliley Act, see our GLBA Compliance: Overview, Privacy, and Safeguards Rule guide →
SEC Regulation S-P
SEC Regulation S-P applies to broker-dealers, investment advisors, and investment companies. It focuses on how these firms protect customer information and communicate their privacy practices.
Like GLBA, Regulation S-P requires firms to adopt written policies that address the protection of nonpublic personal information. For example, a registered investment advisor needs procedures for safeguarding client account data and responding to unauthorized access.
Regulation S-P also covers privacy notices and limits on sharing customer information. Firms subject to SEC oversight are often examined on how well their policies match actual practices. Clear documentation and consistent execution matter just as much as having policies in place.
Want a deeper look at how Regulation S-P applies in practice? See our complete guide on Regulation S-P →
State Laws That Supplement GLBA
GLBA sets a federal baseline, but many states add their own privacy and data security requirements. These state laws often expand obligations or introduce stricter standards, especially around data breaches and consumer rights.
For example, some states require faster breach notifications or broader definitions of personal information. A fintech operating nationwide may need to follow multiple state rules at the same time, even if it already complies with GLBA at a high level.
The practical challenge is coordination. Teams need to track which state laws apply based on customer location and business activity. Building flexible policies and response plans helps avoid last-minute scrambling when state regulators get involved.
NPI and International Privacy Regimes
If your company serves customers outside the US, nonpublic personal information may also be subject to international privacy laws. These regimes often overlap with US requirements but introduce their own definitions and expectations.
For example, the General Data Protection Regulation (GDPR) focuses on personal data more broadly, not just financial information. For fintechs with EU customers, this means the same NPI may be regulated under US financial rules and GDPR at the same time, affecting consent, access rights, and data retention practices.
The key is alignment. While the labels differ, many core principles are similar, like limiting access, protecting data, and being transparent.
Learn more about GDPR for financial services →
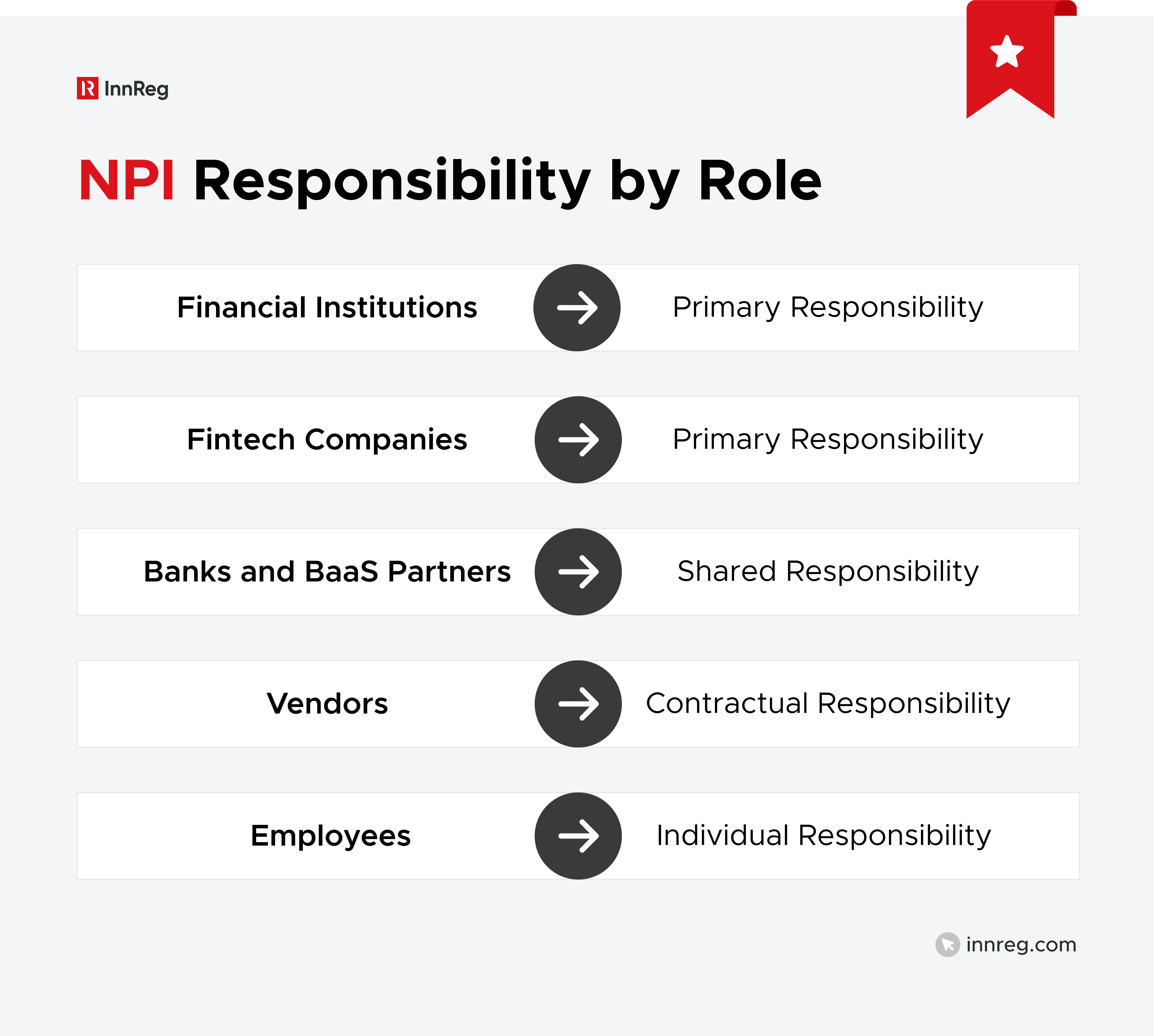
Who Is Responsible for Protecting NPI?
Protecting nonpublic personal information isn’t the responsibility of one team or one role. Anyone who collects, uses, or has access to NPI plays a part in keeping it protected. Regulators expect clear ownership, defined responsibilities, and oversight that matches how data actually flows through the organization.
See also:
Financial Institutions That Collect or Use NPI
Financial institutions that collect or use nonpublic personal information are responsible for protecting it. This includes banks, broker-dealers, investment firms, lenders, payment companies, and many fintechs.
Any company that gathers customer data to open accounts, process transactions, or provide financial services is accountable for how that information is handled. For example, a digital lender that collects income and credit data must safeguard it throughout its lifecycle.
That obligation doesn’t end when data moves across teams or to third parties. Firms are expected to maintain oversight and manage risks tied to how NPI is accessed and used.
Fintech Companies Handling Consumer Financial Data
Fintech companies often handle large volumes of nonpublic personal information, even if they don’t hold customer funds directly. If your product relies on consumer financial data, NPI obligations usually apply.
For example, a budgeting app that pulls transaction data through an API or a crypto platform that collects identity and account details during onboarding is handling NPI. The same is true for platforms that analyze or route financial data behind the scenes.
Being one step removed from the end customer doesn’t change the expectation. Regulators focus on how fintechs access, use, and protect data.
Vendors, Service Providers, and Technology Partners
Vendors and service providers that access nonpublic personal information also carry responsibility for protecting it.
For example, a cloud hosting provider, KYC vendor, or CRM platform may store or process customer financial data. In those cases, the vendor is expected to follow security and confidentiality requirements that match the sensitivity of the information.
Financial institutions are still responsible for oversight, but vendors must meet contractual and regulatory expectations.
Responsibility in Partner and BaaS Relationships
In partner and banking-as-a-service relationships, responsibility for NPI is shared. Each party is accountable for how it accesses, uses, and protects the data, even when roles are split.
For example, a fintech may handle customer onboarding and data collection, while a partner bank holds accounts and processes transactions. Both parties touch NPI, so both need controls, policies, and oversight tied to their specific activities.
Regulators closely scrutinize these arrangements. They expect clear agreements that spell out data responsibilities and ongoing coordination between partners.
Shared and Downstream Responsibility for NPI
NPI often moves beyond the team that first collects it. Responsibility follows the data, even as it flows to other departments, affiliates, or vendors.
For example, customer data collected during onboarding may later be accessed by compliance, support, analytics, or external service providers. Each party that touches that data is expected to handle it appropriately.
This is where gaps tend to appear. Companies may secure NPI at the front end but lose visibility downstream. Mapping data flows and setting clear access rules helps teams manage that risk without slowing down the business.
Core Compliance Obligations for Nonpublic Personal Information (NPI)
Most NPI requirements come down to a few core obligations. Regulators want to see clear rules around how data is disclosed, shared, and protected. Here are the expectations that show up most often in exams and enforcement actions.
1. Privacy Notices and Required Disclosures
Privacy notices explain how your company collects, uses, and shares nonpublic personal information. They’re a core requirement under GLBA and similar rules, and regulators pay close attention to them.
A good privacy notice tells customers:
What information you collect
Who you share it with
Why it’s being shared
For example, if you use third-party vendors for processing or analytics, that sharing should be clearly described.
Problems usually arise when notices don’t match reality. Therefore, if your data practices change, your disclosures need to change, too.
2. Limits on Sharing and Use of NPI
Nonpublic personal information can’t be shared or used without limits. Even when sharing feels operationally necessary, regulations restrict how NPI is disclosed and for what purposes.
For example, sharing customer data with a service provider to process transactions is usually permitted. Using that same data for unrelated marketing or selling it to third parties often isn’t. The purpose of the sharing matters.
Teams should document why NPI is shared, who receives it, and how it’s used. Clear boundaries help prevent misuse and make it easier to explain data practices during exams.
3. Consumer Opt-Out Rights
In some situations, consumers have the right to opt out of certain types of nonpublic personal information sharing. These rights usually apply when data is shared outside permitted operational purposes.
For example, if a company shares customer information with third parties for marketing, customers may have the right to opt out of that sharing. On the other hand, sharing NPI with vendors that support core services often doesn’t trigger opt-out rights.
What matters is clarity. Companies need to understand when opt-out rights apply and how they’re offered.
4. Safeguarding Nonpublic Personal Information
Protecting nonpublic personal information starts with a few core practices. Regulators often focus on how access is managed, how much data is collected, and how third parties are controlled. These safeguards should reflect how NPI actually flows through your organization, not just what’s written in policy.
Access Controls
Access to NPI should be limited to people who need it to do their jobs. This reduces risk and makes it easier to spot unusual activity.
For example, customer support may need to view basic account details, while only compliance or finance teams should have access to full transaction histories. Role-based access helps keep data exposure narrow and intentional.
Data Minimization
Data minimization means collecting and keeping only the information you actually need. Holding on to extra data increases risk without adding value.
If a product no longer requires certain customer details, that information shouldn’t sit unused in your systems. Less data means fewer places for problems to occur.
Vendor and Third-Party Oversight
Vendors that touch NPI need oversight, not just contracts. Companies should understand what data vendors access and how they protect it.
For example, a KYC provider or cloud service may store sensitive customer information. Clear security expectations, due diligence, and periodic reviews help manage that risk.
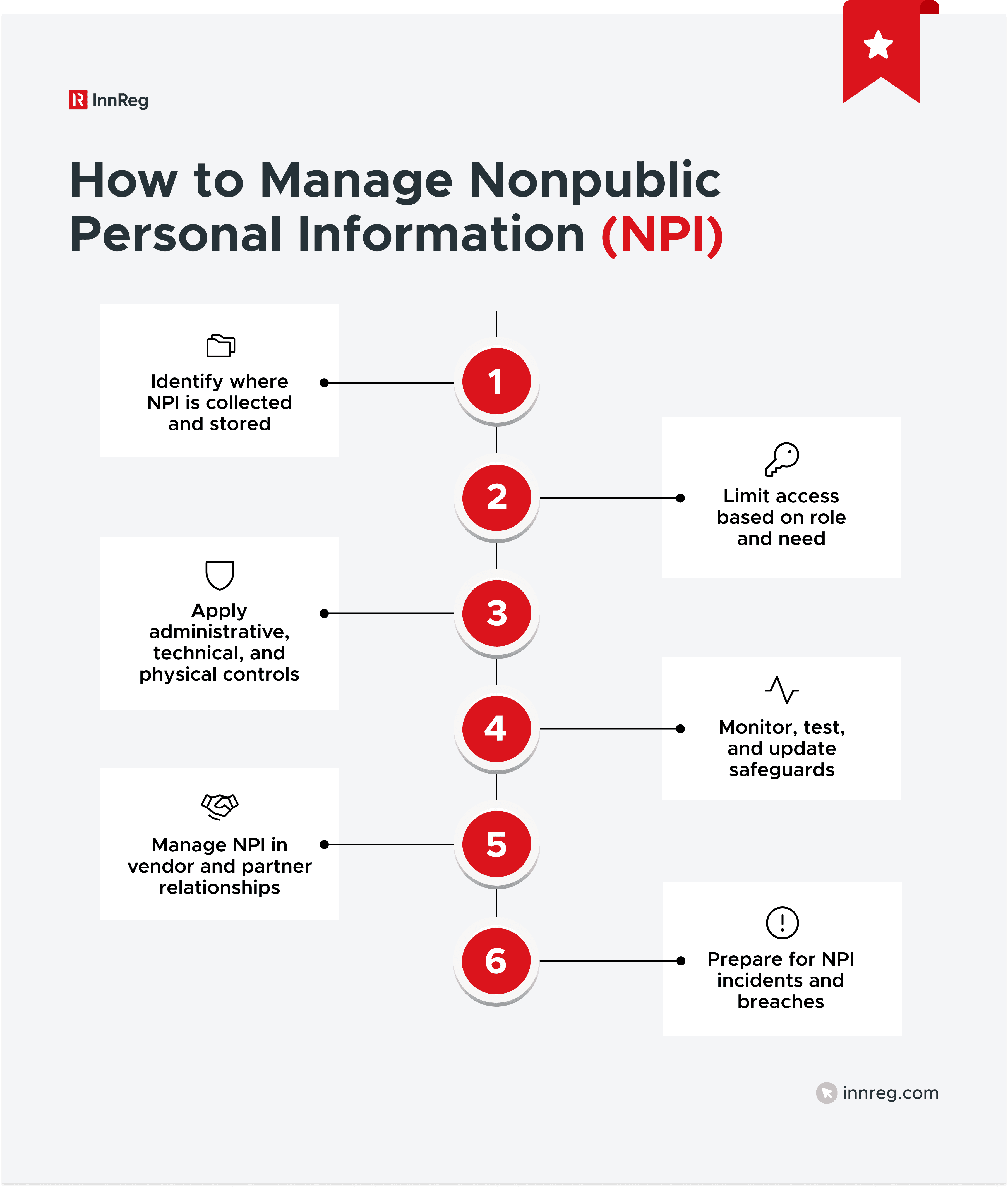
How to Manage Nonpublic Personal Information (NPI)
Managing nonpublic personal information is an ongoing process, not a one-time setup. Teams need clear visibility into where data lives, who can access it, and how it’s protected over time. The steps below focus on practical actions that help companies manage NPI without slowing operations.
See also:
1. Identify Where NPI Is Collected and Stored
The first step in managing nonpublic personal information is knowing where it exists. You can’t protect data you can’t see.
NPI often lives in more places than teams expect, including onboarding forms, internal tools, shared drives, ticketing systems, analytics platforms, and vendor systems.
Creating a simple data map helps. It shows where NPI enters the business, where it’s stored, and who can access it. That visibility makes every other control easier to design and maintain.
2. Limit Access to NPI Based on Role and Need
Not everyone in your organization needs access to nonpublic personal information. Limiting access based on role reduces risk and keeps data exposure under control.
For example, engineers may need system-level access without seeing customer identities, while support teams might need limited visibility to help users. Giving broad access “just in case” creates unnecessary risk.
Regular access reviews help keep permissions current. When roles change or employees leave, access should change too. Small adjustments like this go a long way in protecting NPI.
3. Protect NPI With Administrative, Technical, and Physical Controls
Protecting nonpublic personal information takes more than one type of control. Regulators expect a mix of administrative, technical, and physical safeguards that work together.
This often starts with administrative controls like policies, procedures, and training, so employees know how to handle customer data and what to do when something looks off. Technical controls then support those rules through measures like authentication, logging, and encryption. Physical controls add another layer, such as locked offices or restricted server access.
The goal isn’t complexity. It’s coverage. When these controls align with how your teams actually work, NPI protection becomes part of normal operations rather than a separate compliance task.
4. Monitor, Test, and Update NPI Safeguards
Safeguards around nonpublic personal information need ongoing attention. Controls that worked last year may not match today’s systems or risks.
That’s why regular review matters. Monitoring access logs, testing incident response plans, and updating policies on a set schedule help keep protections current.
Updates don’t have to be complex. Small, regular check-ins help teams catch gaps early and show regulators that safeguards are actively managed.
5. Manage NPI in Vendor and Partner Relationships
Vendors and partners often have access to nonpublic personal information, which means their controls matter too. Sharing data doesn’t shift responsibility away from your company.
Clear contracts help, but oversight matters just as much. Periodic reviews, security questionnaires, and clear escalation paths make it easier to manage risk as relationships evolve.
6. Prepare for NPI Incidents and Breaches
Even with strong controls, incidents involving nonpublic personal information can happen. Regulators care less about perfection and more about how teams respond.
Preparation starts with a clear incident response plan. Teams should know who to notify, what steps to take, and how decisions are documented. For example, if an unauthorized user accesses customer data, staff should know how to contain the issue and escalate it quickly.
Enforcement, Exams, and Penalties Related to NPI
Regulators regularly review how companies handle nonpublic personal information. Exams and enforcement actions often focus on whether controls match actual practices.
Understanding how regulators approach NPI enforcement helps teams prepare more effectively and reduce surprises during reviews.
Regulatory Exams and Findings
NPI issues often come up during routine regulatory exams. Examiners look for gaps between written policies and how data is actually handled.
Common findings include outdated privacy notices, overly broad access to customer data, or weak vendor oversight. For example, a firm may have strong policies on paper but allow too many employees to view full customer records.
A little preparation goes a long way. Keeping data flows documented, regularly reviewing who has access, and testing controls makes it much easier to respond to questions and resolve issues without slowing the business down.
Civil Penalties and Consent Orders
When regulators find serious or repeated NPI issues, enforcement actions can follow. These often take the form of civil penalties or consent orders that require corrective action.
These situations don’t just affect the bottom line. They can also take up a lot of time and energy that’s better spent growing the business. Catching and fixing gaps early makes compliance smoother and helps avoid headaches down the road.
Individual Accountability
Responsibility for protecting nonpublic personal information doesn’t stop at the company level. Individuals can also be held accountable for how NPI is handled.
Compliance officers, executives, and employees with data access may face scrutiny if they ignore policies or fail to escalate issues. For example, intentionally allowing improper access to customer data can lead to personal consequences.
Clear roles, training, and escalation paths help reduce that risk. When people understand their responsibilities, NPI protection becomes part of daily decision-making rather than an afterthought.
—
Nonpublic personal information shows up across nearly every part of a financial services business. Understanding what counts as NPI and how it’s regulated helps teams make better decisions day to day, not just during exams.
Strong programs build on that understanding. They focus on visibility, clear ownership, and practical controls that match how the business actually operates, making it easier to work with regulators, vendors, and partners as products and data flows evolve.
How Can InnReg Help?
InnReg is a global regulatory compliance and operations consulting team serving financial services companies since 2013.
We are especially effective at launching and scaling fintechs with innovative compliance strategies and delivering cost-effective managed services, assisted by proprietary regtech solutions.
If you need help with compliance, reach out to our regulatory experts today:
Related Articles









