What Is Personally Identifiable Information (PII)? A Full Guide
·
18 min read
Every fintech collects personally identifiable information within seconds of a user’s first interaction. From names entered during signup to addresses used for identity verification and bank accounts linked for funding, each data point carries regulatory implications.
In financial services, how data is handled matters as much as why it's collected. Regulators expect firms to know what personal data they hold, where it's stored, and who has access to it. Gaps in these controls can create compliance risk, even when the product itself is otherwise compliant.
In this guide, you’ll learn what personally identifiable information is and why it matters for fintech companies. We’ll also highlight what regulators expect firms to understand before making decisions about data handling, controls, and oversight.
At InnReg, we help fintech and financial services companies manage compliance obligations tied to personally identifiable information. From data inventories and policies to vendor oversight and ongoing compliance operations, our team supports firms handling PII across regulated environments.
What Is Personally Identifiable Information (PII)?
Personally Identifiable Information (PII) is any information that can be used to identify a specific individual, either on its own or when combined with other data.
Common examples of PII include:
Full legal name
Social Security number or tax identification number
Government-issued identification, such as a passport or driver’s license
Email address tied to an account or login activity
Device identifiers connected to a specific user or transaction
The key factor is how the information is used. If a firm or its vendors can use the data to identify an individual, regulators are likely to treat it as PII, even when no single data point appears sensitive on its own.
Examples of PII in Financial Services and Fintech
In financial services and fintech, PII shows up across multiple systems, vendors, and business processes. Here are the common categories of personally identifiable information.
Direct Identifiers
Direct identifiers are forms of personally identifiable information that can identify an individual on their own, without needing any additional data. In financial services, these data points are often required to meet KYC, AML, and customer verification requirements.
Direct identifiers are typically collected during onboarding or account setup. For example, a broker-dealer may request a Social Security number to verify identity, while a lender may collect a government-issued ID to meet underwriting and fraud prevention requirements.
Once collected, these identifiers come with handling and access expectations.
Common direct identifiers in fintech and financial services include:
Full legal name
Social Security number or tax identification number
Government-issued identification, such as a passport or driver’s license
Date of birth
Residential address
Because direct identifiers clearly point to a specific person, they are closely monitored by regulators and are often subject to stricter internal controls. Firms are expected to know where this information is stored, who can access it, and how it's protected throughout its lifecycle.
Indirect Identifiers
Indirect identifiers are pieces of information that don’t identify a person by themselves but can do so when combined with other data. In fintech, these data points often seem routine, making them easy to overlook.
For example, an IP address or device ID may not seem personal on its own, but when linked to an account or transaction activity, it can point back to a specific individual.
Common examples of indirect identifiers in financial services include:
Email address
Phone number
IP address
Device identifiers
Account numbers or user IDs
Because indirect identifiers gain meaning through context, their risk often increases as systems and data sources are connected.
Firms are expected to understand how these data points interact across platforms, vendors, and internal tools, especially as products scale and data use becomes more complex.
Sensitive vs. Non-Sensitive PII
Not all personally identifiable information carries the same level of risk. Some PII can cause significant harm if misused, while other data is lower risk on its own. This distinction is often described as sensitive versus non-sensitive PII, and it matters for how information is handled and protected.
Sensitive PII includes data that could lead to identity theft, financial loss, or serious privacy harm if exposed.
Think of Social Security numbers, bank account details, or copies of government-issued IDs. Non-sensitive PII, such as a name or email address, may seem less risky, but can still create exposure when combined with other data points.
The difference is not always obvious.
A single data point may be non-sensitive in isolation but become sensitive in context. For example, a customer’s name alone is typically low risk, but that same name paired with account access details or transaction history raises the stakes.
Here’s a table to illustrate the difference:
Type of PII | Examples | Risk Considerations |
|---|---|---|
Sensitive PII | Social Security numbers, bank account numbers, government IDs | Higher risk of identity theft and financial harm |
Non-sensitive PII | Names, email addresses, phone numbers | Lower risk individually, higher risk when combined |
PII vs. Nonpublic Personal Information (NPI): What's the Difference?
Personally identifiable information and nonpublic personal information are often used interchangeably, but they are not the same thing.
Nonpublic personal information generally refers to personal data that a financial institution collects in connection with providing a financial product or service.
This includes:
Information a customer provides on an application
Data generated through transactions
Details obtained from third parties.
For example, a customer’s account balance or transaction history may qualify as NPI even if it's not always treated as PII in other contexts.
The key difference lies in scope and purpose. PII focuses on identifiability, while NPI focuses on customer relationships and confidentiality obligations.
A name and email address may be PII, but not NPI if no financial relationship exists. Once that same information is tied to an active account, it's more likely to be treated as NPI under financial privacy rules.
Understanding this distinction matters. Firms subject to rules like GLBA must apply specific safeguards to NPI, even when similar data might be treated differently under broader privacy frameworks.
Knowing when information crosses from PII into NPI helps teams apply the right controls and avoid regulatory missteps.
Category | PII | NPI |
|---|---|---|
Regulatory scope | Broad privacy and data protection frameworks | Financial services–specific privacy rules |
Example data | Name, email address, phone number | Account numbers, balances, transaction history |
When it applies | When data can identify a person | When a customer relationship exists |
Common regulations | State privacy laws, GDPR | GLBA and related rules |
Why PII Matters for Fintechs and Financial Institutions
Personally identifiable information plays a central role in how financial services operate. It supports compliance obligations, customer interactions, and internal decision-making. When PII is poorly managed, the resulting risk often cuts across multiple regulatory and operational areas.
For fintechs and financial institutions, PII matters because it:
Directly affects regulatory oversight: Regulators expect firms to understand what personal data they collect, how it's used, and who can access it. Gaps in data mapping or ownership often surface during examinations.
Shapes examination and enforcement outcomes: Weak controls around PII, such as excessive employee access or limited vendor management, can lead to findings even when no breach has occurred.
Protects customers from real-world harm: Exposure of personal data can lead to identity theft, unauthorized transactions, or misuse of financial accounts, all of which regulators take seriously.
Influences customer and partner trust: Fintechs rely on confidence from users, banks, and counterparties. Poor data handling can undermine those relationships and slow growth initiatives.
Impacts vendor and third-party risk: Many fintechs rely on vendors to process or store PII. Firms remain responsible for how that data is handled, even when it sits outside their systems.
Becomes harder to manage as products scale: As new features, jurisdictions, and integrations are added, PII often spreads across more systems. Without clear controls, risk increases as growth accelerates.
Understanding these pressures helps teams treat PII as a core compliance consideration, not a standalone privacy issue.
See also:
Who Regulates PII? Key US and Global Authorities
A mix of financial regulators, consumer protection agencies, and data privacy authorities oversees personally identifiable information. The rules that apply depend on a firm’s business model, where it operates, and the types of data it handles, often resulting in overlapping expectations.

Need help with fintech compliance?
Fill out the form below and our experts will get back to you.
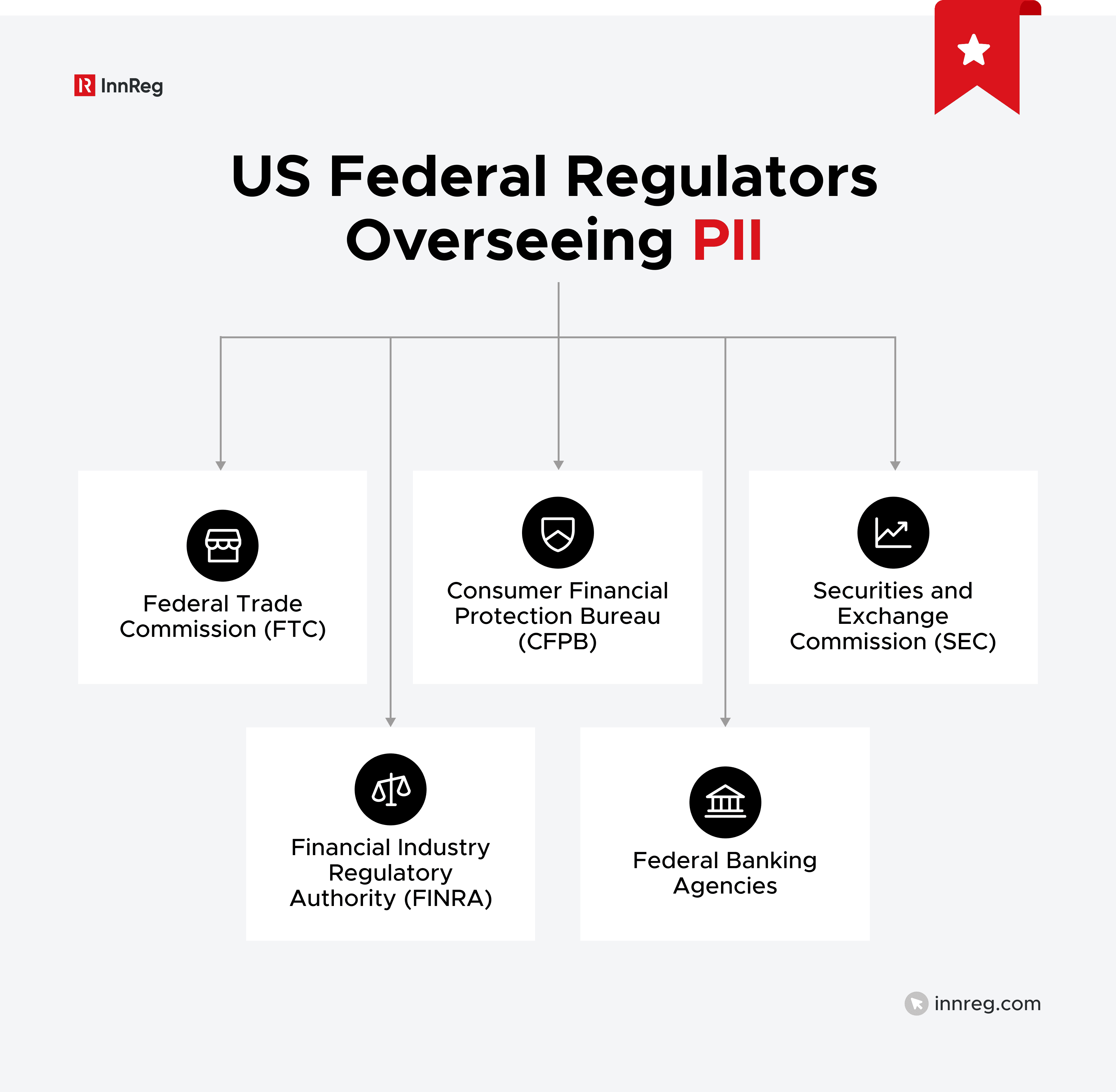
Federal Regulators (US)
In the US, several federal regulators share responsibility for enforcing PII. Each looks at PII through the lens of its own mandate, such as investor protection, consumer financial protection, or market integrity. For many fintechs, this means more than one federal regulator may have a say in how PII is handled.
For instance, a broker-dealer registered with the SEC and FINRA is expected to safeguard customer records, while a lender or payments company may be examined by agencies focused on consumer protection.
Even firms that don't consider themselves data-driven businesses are still expected to understand how personal information moves through their systems.
Here’s how key US federal regulators approach PII and what that means for regulated financial institutions.
Federal Trade Commission (FTC)
The Federal Trade Commission (FTC) plays a broad role in protecting personally identifiable information across the US economy.
For many fintechs, the FTC becomes relevant when a company handles consumer data outside traditional securities or banking supervision. In those cases, the agency looks at whether personal data is handled in ways that are fair, transparent, and consistent with what the firm tells users.
That oversight is rooted in the FTC’s authority to police unfair or deceptive acts or practices. When a fintech claims user data is protected but fails to follow its own policies, the mismatch can draw regulatory attention.
For example, storing customer information in unsecured systems or granting access beyond what is disclosed to users may raise concerns.
Unlike sector-specific regulators, the FTC doesn't prescribe a single compliance framework. Instead, it looks closely at a company’s actual practices, disclosures, and controls. This makes documentation, internal policies, and vendor oversight especially important for fintechs operating under the FTC’s scope.
Consumer Financial Protection Bureau (CFPB)
The Consumer Financial Protection Bureau (CFPB) oversees how consumer financial data is handled across lending, payments, and other consumer-facing financial products.
For fintechs, the CFPB often becomes relevant when PII is collected or used in ways that affect consumers’ access to financial services. That oversight is grounded in the agency’s consumer protection authority.
Issues can arise when personal data is:
Inaccurate
Shared without appropriate controls
Maintained in ways that lead to errors in credit decisions or account servicing
For example, incorrect customer data flowing through underwriting or billing systems can raise both privacy and consumer protection concerns.
Rather than treating PII as a standalone issue, the CFPB views data handling as part of the broader customer experience. Fintechs are expected to understand how personal information supports disclosures, decision-making, and ongoing account management, especially when third-party vendors are involved.
Securities and Exchange Commission (SEC)
The Securities and Exchange Commission (SEC) regulates how registered investment advisors, broker-dealers, and other market participants handle customer information. For firms under its oversight, PII is closely tied to recordkeeping, supervision, and safeguarding obligations.
The SEC expects firms under its oversight to maintain controls around how personal data is collected, stored, and accessed. This includes customer records, account documentation, and communications that contain identifying information.
For example, giving too many employees access to client files or failing to keep track of how third-party vendors handle data can raise concerns during an examination.
PII also comes into play as part of cybersecurity and operational risk. Weak data controls can signal broader supervisory gaps, especially when personal information is exposed through system vulnerabilities or inconsistent internal practices.
As a result, firms are expected to treat customer data as part of their overall compliance and risk management framework.
Financial Industry Regulatory Authority (FINRA)
FINRA oversees how broker-dealers protect customer information as part of its broader supervision and recordkeeping responsibilities. For member firms, this places PII squarely within the requirements related to customer records, supervision, and cybersecurity.
As a result, FINRA rules and guidance focus on whether firms maintain reasonable controls over the use and access of personal data. These expectations include:
Limiting internal access to customer records
Monitoring system permissions
Overseeing vendors that handle client information
For example, a firm that allows registered representatives to download customer data to personal devices may raise supervisory concerns.
PII is also a focal point during FINRA examinations, particularly when policies exist on paper but are not actually followed. In those cases, regulators expect firms to show that controls around customer information are both documented and enforced.
Federal Banking Agencies
For banks and bank-affiliated fintechs, oversight of personally identifiable information comes from federal banking regulators such as the:
These regulators review how PII is handled across multiple areas, including information security programs, third-party risk management, and internal controls. That review often goes beyond written policies.
Banking regulators also assess whether data protection practices are actually working in day-to-day operations, especially when vendors, cloud providers, or offshore teams are involved.
State-Level Authorities
State authorities often step in where federal rules leave gaps, especially around:
Data privacy
Cybersecurity
Consumer protection
For companies operating across multiple states, this layer of oversight can add real complexity. State regulators may review how PII is handled as part of licensing, examinations, or enforcement actions, and expectations can vary by jurisdiction.
For example, a money transmitter licensed in several states may face different data security requirements depending on where its customers are located. State laws may also impose specific notification and remediation obligations if personal data is compromised.
State Attorneys General
Unlike federal financial regulators, State Attorneys General often step in after an issue has surfaced, such as a data breach or a pattern of consumer complaints. Their focus is typically on consumer harm and whether a company’s practices violate state privacy or consumer protection laws.
For fintechs, investigations by a State Attorney General can arise from how personal data is managed across products, systems, and vendors. For example, failing to disclose how customer information is used or delaying required breach notifications may prompt enforcement action.
These cases often draw public attention and can involve coordination across multiple states.
California Privacy Protection Agency (CPPA)
The California Privacy Protection Agency (CPPA) is the primary regulator responsible for enforcing California’s consumer privacy laws.
For fintechs with customers in California, the CPPA plays a direct role in how personally identifiable information is handled. Its authority applies regardless of where a company is headquartered, as long as California residents are involved.
The CPPA focuses on transparency and data rights. This includes how firms:
Disclose their data practices
Respond to consumer requests
Limit the use of personal information to stated purposes
Unlike broader state enforcement bodies, the CPPA is dedicated solely to privacy oversight. That focus means fintechs should expect detailed scrutiny of data inventories, internal controls, and vendor arrangements when California privacy requirements apply.
New York Department of Financial Services (NYDFS)
The New York Department of Financial Services (NYDFS) monitors how financial institutions protect customer information as part of its broader focus on safety, soundness, and consumer protection.
For fintechs licensed or operating in New York, this means PII is often reviewed through cybersecurity and operational risk requirements.
NYDFS expects covered entities to maintain structured programs that address:
Data security
Access controls
Incident response
This includes limiting who can view customer records and monitoring systems that store personal data. When controls are weak or responses to security incidents are delayed, regulatory attention often follows.
International Data Protection Authorities
Fintechs with international operations or customers are often subject to data protection oversight outside the US. In these cases, personal data may be regulated by foreign authorities with their own privacy frameworks and expectations.
Here are some of the key regulators involved.
European Union: Supervisory Authorities under GDPR
National supervisory authorities in the European Union enforce data protection under the General Data Protection Regulation (GDPR). For fintechs that serve EU residents, GDPR applies even when the company itself is based outside the EU.
Those authorities look closely at whether firms have a lawful basis for using personal data and whether their practices match what is disclosed to users. For example, collecting customer information for onboarding doesn’t automatically allow that data to be reused for analytics or marketing.
GDPR also places strong emphasis on individual rights. Firms must, therefore, be prepared to respond to requests related to access, correction, and deletion of personal data.
United Kingdom: Information Commissioner's Office (ICO)
In the United Kingdom, the Information Commissioner’s Office (ICO) regulates how organizations handle personally identifiable information. This oversight directly informs data protection and privacy expectations for fintechs operating in or targeting the UK market.
The ICO places strong emphasis on fairness and transparency in how personal data is used. Firms are expected to clearly explain what data they collect, why it is collected, and how long it is retained.
For example, keeping customer information indefinitely without a clear business or regulatory reason can raise compliance concerns.
The ICO also takes a practical view of risk. It looks at whether firms have appropriate controls in place to prevent misuse or unauthorized access to personal data.
Canada: Office of the Privacy Commissioner (OPC)
In Canada, the Office of the Privacy Commissioner (OPC) oversees how organizations handle personal information across the private sector. For fintechs, this oversight centers on accountability and purpose limitation.
Firms are expected to collect only the information they need and to use it in ways that align with customer expectations.
The OPC also looks closely at how organizations manage third-party relationships. When vendors process or store personal information, the responsibility remains with the fintech.
Asia-Pacific Regulators
National data protection authorities enforce PII across the Asia-Pacific region. These regulators often set clear expectations around data localization, security, and cross-border transfers, which can shape how fintechs design and operate their products.
Oversight looks different from country to country. For example:
China: Regulators such as the Cyberspace Administration of China (CAC) pay close attention to where personal data is stored and whether it can be transferred outside the country.
Singapore: The Personal Data Protection Commission (PDPC) expects firms to have clear, well-defined policies for how personal data is used and how long it is kept.
Australia: The Office of the Australian Information Commissioner (OAIC) focuses on whether firms are taking reasonable steps to protect personal information from misuse or unauthorized access.
For fintechs expanding into Asia-Pacific markets, PII compliance often benefits from early planning and local insight. Understanding how regional rules affect product design, vendor choices, and infrastructure decisions can help avoid surprises later on.
Common Compliance Challenges with Personally Identifiable Information
As fintechs grow, managing personally identifiable information can become more complex. In most cases, PII challenges stem from everyday operational gaps rather than intentional misuse.
Common compliance challenges include:
Data sprawl across systems: PII is often spread across onboarding tools, transaction systems, CRMs, and third-party platforms. When firms lack a clear data inventory, it becomes harder to control access or respond to regulatory inquiries.
Overly broad or outdated access permissions: Employees may retain access to customer data after changing roles or responsibilities. Without regular reviews, unnecessary access can quietly increase risk.
Limited visibility into vendor data practices: Many fintechs rely on vendors to process or store PII. Weak oversight or unclear contracts can leave firms exposed, even when data never touches internal systems.
Inconsistent policies and real-world practices: Written procedures may describe strong controls, but day-to-day execution doesn't always match. Regulators often focus on this gap during exams.
Cross-border data complexity: Serving customers in multiple jurisdictions can trigger overlapping privacy and data transfer requirements that are difficult to manage without coordination.
Delayed incident response and reporting: When PII issues occur, slow detection or unclear escalation paths can worsen regulatory and operational outcomes.
Understanding these challenges helps firms identify where controls tend to break down and where additional oversight may be needed.
Best Practices for Managing PII in Fintech
Managing personally identifiable information works best when controls are practical and built into everyday operations. The goal is not perfection, but consistency, visibility, and accountability.
Key best practices include:
Maintain a clear inventory of PII: Know what personal data you collect, where it's stored, and how it moves across systems. For example, mapping which vendors receive customer data can quickly surface hidden risk.
Limit access based on role and need: Only employees who need PII to perform their job should have access. Periodic access reviews help prevent outdated permissions as teams and responsibilities change.
Build PII controls into onboarding and product design: Collect only what is necessary and document why it's needed. This reduces exposure and makes it easier to explain data practices to regulators.
Apply consistent oversight to third-party vendors: Vendors often process large volumes of PII. Clear contracts, defined responsibilities, and ongoing monitoring help firms stay accountable for how customer data is handled.
Align policies with actual practices: Written procedures should reflect how systems and teams operate in reality. Regulators often focus on gaps between policy and execution.
Prepare for incidents before they happen: Clear escalation paths, internal ownership, and response procedures make it easier to manage PII issues quickly and consistently.
Together, these practices help fintechs manage PII as an ongoing operational responsibility, not a one-time compliance task.
What Happens When PII Is Breached? Legal and Operational Fallout
A breach involving personally identifiable information rarely stays contained. Even a limited exposure can lead to consequences that extend well beyond the initial incident, including:
Regulatory impact: Firms may face reporting obligations and follow-up inquiries. Depending on the data involved and where affected individuals are located, multiple regulators may need to be notified.
Operational disruption: Incident response often diverts internal resources and interrupts normal workflows. Temporary system restrictions, vendor changes, customer communications, and internal investigations can quickly stretch already lean teams.
Reputational risk: While harder to measure, reputational impact is real. Customers and partners expect financial institutions to handle personal data responsibly, and a breach can raise questions about controls, oversight, and trust, even after technical issues are resolved.
See also:
Misconceptions About PII That Get Fintechs in Trouble
Misunderstandings about personally identifiable information often create risk long before a regulator gets involved. These assumptions tend to feel practical in the moment but fall apart under scrutiny.
Common misconceptions include:
Only highly sensitive data counts as PII: Many teams focus solely on Social Security numbers or bank details. In reality, email addresses, device IDs, and account identifiers can also be treated as PII when they link back to an individual.
Data becomes safer once it's anonymized or tokenized: While these techniques reduce risk, they don't always remove it. If data can still be reconnected to a person through other systems or keys, regulators may continue to treat it as PII.
Vendors are responsible once data is shared: Fintechs often assume compliance responsibility shifts to third parties. Regulators consistently hold firms accountable for customer data, even when vendors store or process it.
Strong policies are enough on their own: Written procedures matter, but regulators focus on execution. When day-to-day practices don't match documentation, that disconnect becomes a problem.
PII risk only increases after a breach: Many findings arise without any breach at all. Excessive access, weak oversight, or poor documentation can trigger issues on their own.
Controls that worked early will scale automatically: As products, teams, and integrations grow, PII often spreads across more systems. Controls need to evolve alongside the business.
Addressing these misconceptions helps firms manage PII proactively rather than reactively.
—
Personally identifiable information is more than a data issue. It is a regulatory, operational, and trust issue that touches nearly every part of a fintech’s business. How PII is handled, from onboarding and transactions to vendor relationships and exams, shapes how regulators and customers see a firm.
For fintechs in regulated environments, the goal is clarity and consistency. Knowing what data you collect, why you collect it, and how it is protected helps teams stay ahead as products scale and expectations grow. PII management works best when it is treated as an ongoing compliance discipline, not a one-time task.
FAQ: Personally Identifiable Information (PII) in Fintech
Where can PII be found?
PII can be found anywhere a fintech collects or processes customer information. This includes onboarding forms, transaction systems, customer support tools, marketing platforms, and internal reporting dashboards. It can also exist in vendor environments, such as identity verification providers or cloud storage systems.
Is a phone number PII?
Yes. A phone number is considered PII because it can be used to identify or contact a specific individual. When it's linked to an account, login activity, or customer profile, regulators are likely to treat it as personally identifiable information.
What are the top 3 big data privacy risks?
The most common risks involve unauthorized access, excessive data collection, and poor vendor oversight. For example, granting broad system access to employees, collecting more data than necessary, or failing to monitor third parties that process PII can all increase exposure.
What are the 7 personal data protection principles?
While frameworks vary, the core principles generally include lawful and transparent data use, purpose limitation, data minimization, accuracy, storage limitation, security, and accountability. These principles guide how personal data should be collected, used, and protected throughout its lifecycle.
How Can InnReg Help?
InnReg is a global regulatory compliance and operations consulting team serving financial services companies since 2013.
We are especially effective at launching and scaling fintechs with innovative compliance strategies and delivering cost-effective managed services, assisted by proprietary regtech solutions.
If you need help with compliance, reach out to our regulatory experts today:
Related Articles









